MS SQL Maestro online Help
| Prev | Return to chapter overview | Next |
Users
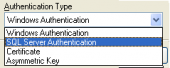
A user passes through two stages of security when working in Microsoft® SQL Server™: authentication and authorization (permissions validation). The authentication stage identifies the user using a login account and verifies only the ability to connect to an instance of SQL Server. If authentication is successful, the user connects to an instance of SQL Server. The user then needs permissions to access databases on the server performed by granting access to an account in each database, mapped to the user login.
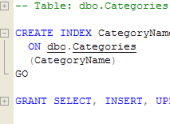
Every database cluster contains a set of database users. Those users are separate from the users managed by the operating system under which the server runs. Users own database objects (for example, tables) and can assign privileges on those objects to other users to control who has access to which object.
Note: Use of roles simplifies security administration in databases with a large number of users or with a complex security system.
| Prev | Return to chapter overview | Next |





 Download
Download Buy
Buy